project // hardware
ESP32 DIV 2.1
about
The ESP32 DIV v2.1 is an open-source multi-band wireless testing toolkit by CiferTech, built around the ESP32-S3. It supports WiFi, BLE, 2.4GHz and Sub-GHz frequencies — designed for wireless testing, signal analysis, jamming research and protocol exploration. The v2.1 is modular — a stable core board with a stackable shield via pogo-pin headers, keeping the device thin and expandable.
hardware
features
WiFi
Bluetooth (BLE)
2.4GHz (NRF24 ×3)
Sub-GHz (CC1101)
EAPOL / WPA
Firmware / Hardware
images
// WiFi — packet monitor, real-time waterfall, channel hop 1–13

// BLE — spoofer, scan + clone target advert payload

// Sub-GHz CC1101 — spectrum analyser, 300–930 MHz sweep

// Sub-GHz — jammer, noise burst across 315 / 433 / 868 / 915 MHz

// splash screen — segfault.solutions logo, NeoPixel cyan glow
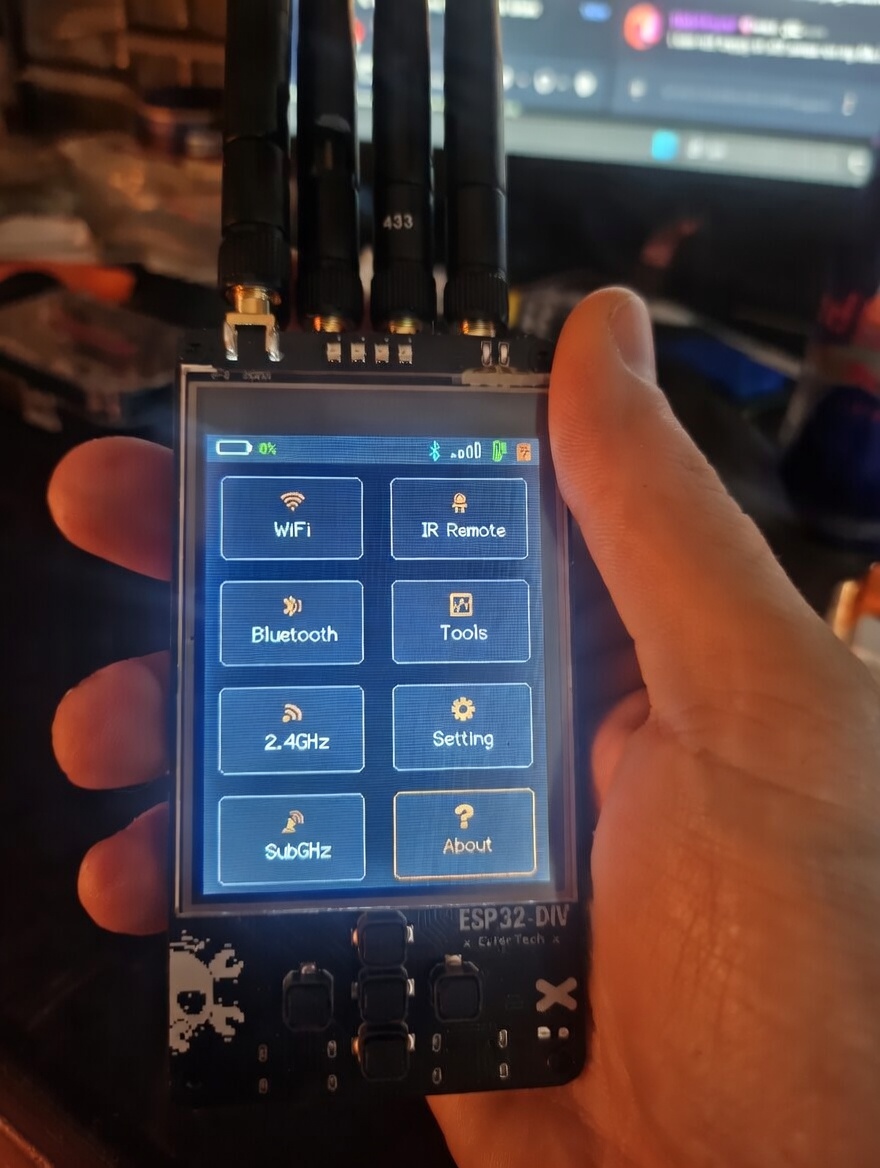
// stock firmware — main menu

// ProtoPirate port — main menu
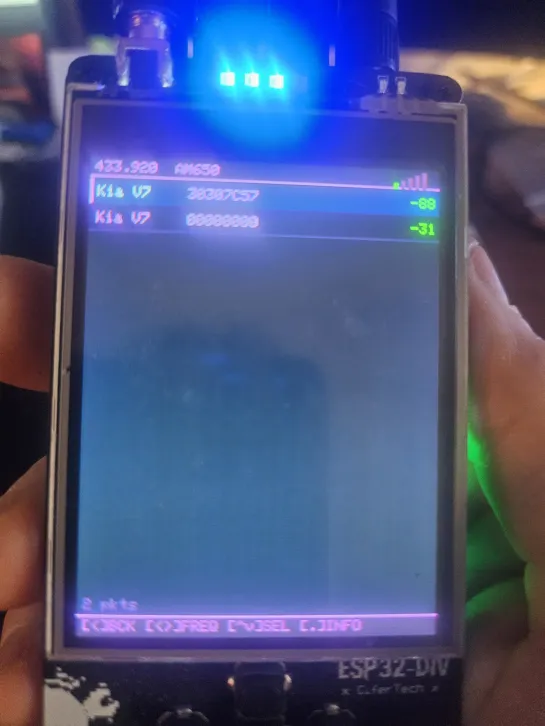
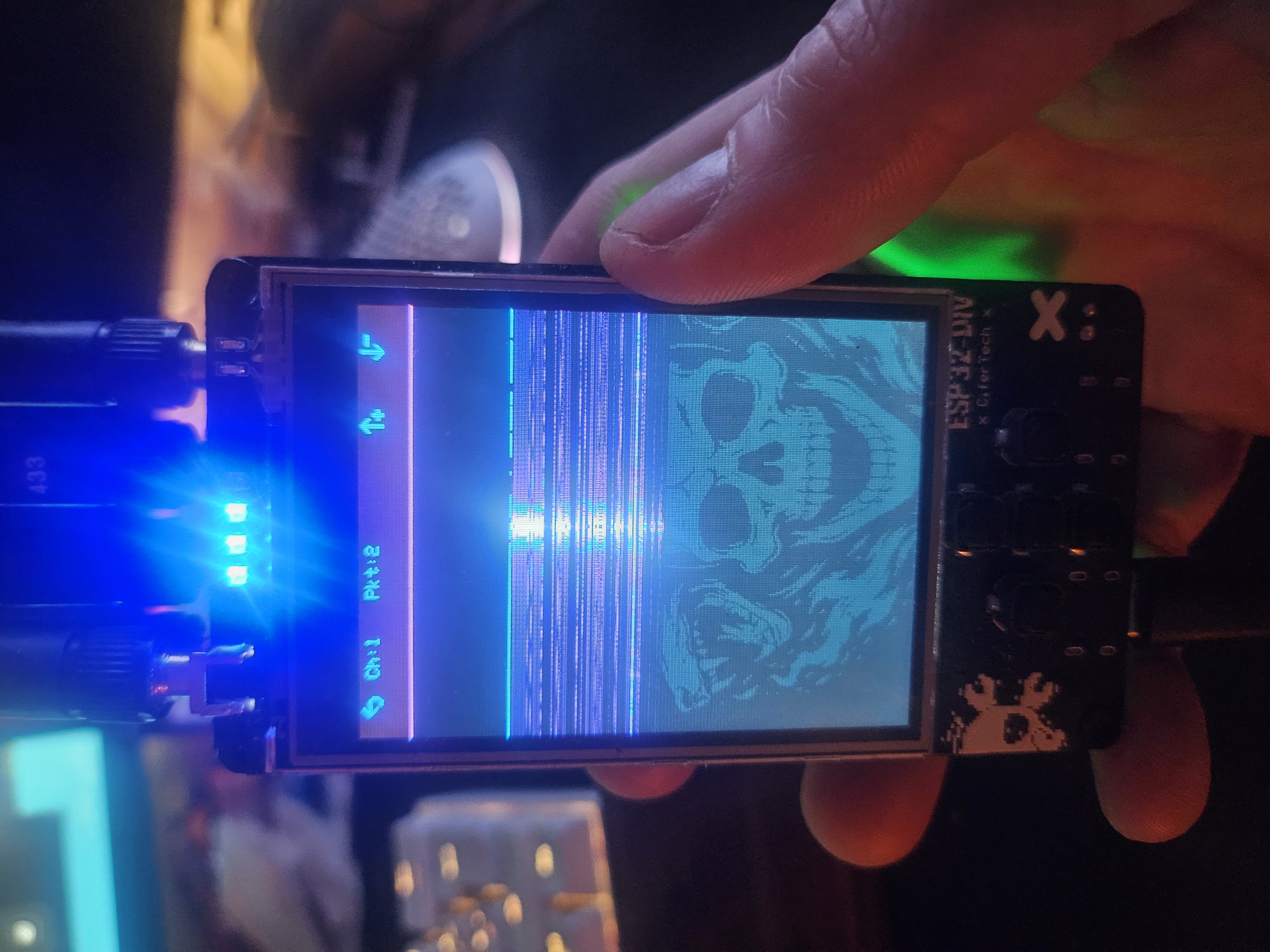
// ProtoPirate — packet list view
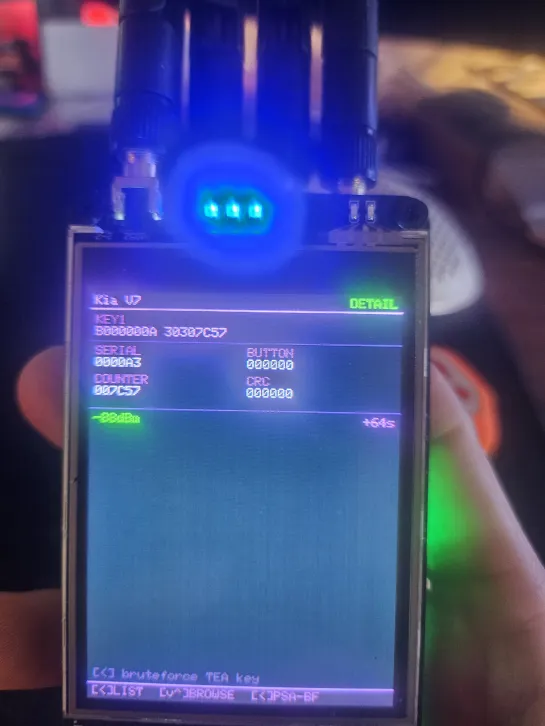
// ProtoPirate — packet detail view
halehound-div firmware
Custom firmware ported from HaleHound-CYD to the ESP32-DIV v2.1 (ESP32-S3). Touch input replaced with PCF8574 GPIO expander at confirmed I2C address 0x27 (M5Shark V2.0 specific — not 0x20 as documented). Display running in portrait 240×320 (rotation=2). SPI bus arbitrated across the display (HSPI dedicated), 3× NRF24 modules, CC1101, and SD card. Boot splash displays for 10 seconds with NeoPixel cyan glow, then serves as the menu background image with transparent item overlay.
huge_app partition scheme, no PSRAMpio run -e esp32s3-div --target uploadpin map
| peripheral | signal | gpio | notes |
|---|---|---|---|
| display | SCK | 36 | HSPI dedicated |
| display | MOSI | 35 | |
| display | MISO | 37 | |
| display | CS | 17 | |
| display | DC | 16 | |
| display | BL | 7 | |
| SDA | 8 | PCF8574 @ 0x27 | |
| SCL | 9 | UP=P7 DOWN=P5 LEFT=P3 RIGHT=P4 CENTER=P6 | |
| NRF24 #1 | CSN | 4 | |
| NRF24 #1 | CE | 15 | |
| NRF24 #2 | CSN | 48 | |
| NRF24 #2 | CE | 47 | |
| NRF24 #3 | CSN | 21 | ⚠ shared with IR RX — held HIGH during capture |
| NRF24 #3 | CE | 14 | ⚠ shared with IR TX — mutex required |
| CC1101 | CS | 5 | |
| CC1101 | GDO0 | 6 | |
| CC1101 | GDO2 | 3 | spi renamed to avoid TFT_eSPI collision |
| SD card | CS | 10 | |
| SD card | Detect | 38 | |
| IR | TX | 14 | ⚠ shared with NRF24 #3 CE |
| IR | RX | 21 | ⚠ shared with NRF24 #3 CSN |
| NeoPixel | DATA | 1 | cyan glow on splash, status indicators |
todo
- 2026-05-30 ✓ done — ProtoPirate SD save + signal replay via CC1101 TX
- 2026-05-30 ✓ done — SD loot saves working — BLE Predator, Flock You, ProtoPirate all saving to SD
- 2026-05-30 ⧗ in progress — BLE Predator GATT recon — connects but service enumeration needs testing
- 2026-05-29 ✓ done — NRF24 #3 fixed — schematic confirmed CE=GPIO14 / CSN=GPIO21 (shared with IR, not GPIO41/42). All 3 NRF24 modules now passing radio test ✅
- 2026-05-21 ⧗ in progress — verify SD loot saves (EAPOL .hc22000, BLE Predator recon log, Flock You output)
-
2026-05-20
✓ done — SD card fixed — was using global
SPIobject instead of dedicatedradioSPIHSPI bus - 2026-05-29 ⧗ in progress — verify SD loot saves (EAPOL .hc22000, BLE Predator recon log, Flock You output) with fixed radioSPI bus
-
2026-05-29
✓ done — BLE Jammer working —
bjRadiolocal RF24 object per namespace,jamSPIcore 0 task usesradioSPI, SELECT/UP/DOWN buttons mapped to toggle/mode change -
2026-05-29
✓ done —
nrf24_config.cppSPI claim/release cleaned up — removedSPI.end()/SPI.begin()pattern, replaced with CS pin management only on sharedradioSPIbus - 2026-05-30 ✓ done — NeoPixel red on attack — all jammers and deauth modules
- 2026-05-30 ✓ done — ProtoPirate Nosifer logo bar in UI
-
2026-05-30
⚠ hardware limit — ESP32-S3 cannot inject raw 802.11 deauth frames —
esp_wifi_80211_tx()blocked at driver level for management frame type 0xC0 -
2026-05-29
⧗ pending —
PCF_BTN_BACK_PINduplicate withPCF_BTN_LEFT_PINon P3 — back button not independent - 2026-05-16 ✓ done — HaleHound modules ported: WiFi (Auth Flood, EAPOL, Karma, Captive Portal), BT+NRF24 (BLE Predator, Lunatic Fringe, Phantom Flood, AirTag Replay, NRF Sniffer, MouseJack), SIGINT (Flock You, WiFi Guardian, BLE Watchdog, SubGHz Sentinel)
- 2026-05-16 ✓ done — test all new modules on-device — button nav confirmed working across all modules after btn_update() cache fix
changelog
-
v1.4 2026-05-30 buttons + SD loot + ProtoPirate replay 18 changes ▶✓ done — ProtoPirate SD save + signal replay via CC1101 TXnew✓ done — SD loot saves working — BLE Predator, Flock You, ProtoPirate all saving to SDnew⧗ in progress — BLE Predator GATT recon — connects but service enumeration needs testingnew✓ done — NeoPixel red on attack — all jammers and deauth modulesnew✓ done — ProtoPirate Nosifer logo bar in UInew⚠ hardware limit — ESP32-S3 cannot inject raw 802.11 deauth frames —hw
esp_wifi_80211_tx()blocked at driver level for management frame type 0xC0button fixes across all modules — audited every attack module for missing PCF8574 button bindings. Fixed: BLE Sniffer (fixhandleTouch()rewritten from touch-only to full button nav — SELECT=scan toggle, UP/DOWN=scroll, LEFT/RIGHT=filter), SubGHz Jammer (SELECT=toggle, LEFT/RIGHT=freq, UP=sweep, DOWN=mode), EAPOL Capture (UP/DOWN=scroll AP list with cursor highlight, SELECT=pick AP, SELECT in capture=deauth toggle). AddedtouchButtonsUpdate()where missing.EAPOL capture button system overhaul — AP list now fully navigable via buttons. Root cause of capture-phase button failures: single event model infixtouch_buttons.h—BTN_BACKcheck consumed the event before capture-phase buttons saw it. Fix: addedinput_read_now()toinput.cpp— direct PCF8574 raw state read bypassing debounce, stored in file-level_capEvforisDeauthTapped()andisSaveTapped(). Deauth toggle (SELECT) and save (UP) now working in capture phase.NRF24 attacks SPI fixed —fixnrf24_attacks.cppwas callingSPI.begin()(global bus) andradio.begin()with no SPIClass pointer. Updated toradio.begin(&radioSPI). Addedshared.hinclude. All NRF24 attack modules now use the correct shared radio SPI bus.NeoPixel attack indicator — addednewneo_attack()(RED) /neo_idle()(OFF) API toshared.h. Hooked into: BLE Jammer (startJamming/stopJamming), SubGHz Jammer (start/stop), WiFi Deauther (initAttackMode/exitAttackMode), EAPOL deauth toggle, NRF24 jammer (nrf_jammer/nrf_stop). NeoPixels go solid red when any attack is active, off when idle.ESP32-S3 raw deauth limitation confirmed —hwesp_wifi_80211_tx()returnsESP_ERR_WIFI_IF (0x102)withunsupport frame type: 0c0on all platform versions tested (espressif32 5.3.0, 6.3.2, 6.13.0). ESP32-S3 WiFi driver blocks raw 802.11 management frame injection at the driver level regardless of IDF version. Affects WiFi Deauther and EAPOL deauth burst. Workaround under investigation (association flood, beacon duplication).ProtoPirate UI — Nosifer logo bar — added persistent "ProtoPirate" title in Nosifer font as a dedicated logo strip between the freq/RSSI header and the packet list content area. Logo appears in all views viafixdraw_header().PP_LOGO_H=28,PP_CONTENT_Yupdated to account for logo height. Splash screen removed — logo is always visible in the UI.BLE Predator + Lunatic Fringe buttons fixed — both modules usedfixbtn_pressed()frombtn_input.hwhich wasn't callingtouchButtonsUpdate(). Fixedbtn_update()inbtn_input.hto calltouchButtonsUpdate(). Added BLE Predator, Lunatic Fringe, Phantom Flood, AirTag Replay to Bluetooth menu — were declared inswitchcases but missing from the items array so unreachable. BLE scan stop added before GATT connect to prevent connect failures.SD loot saves fixed across all modules —fixble_predator.h,flock_you.h,captive_portal.h,iot_recon.hwere callingSD.begin()on an already-mounted card, causing silent failures. Addedextern bool sd_availabletoshared.h. Modules now use the globalsd_availableflag instead of re-initialising SD. ProtoPirate packet saves to/protopirate/<protocol>_<timestamp>.txtconfirmed working.ProtoPirate — SD save + signal replay — addedhwpp_save_packet(): auto-saves every decoded packet to SD. Raw pulse snapshot added toPPPacketstruct (up to 256 pulses). Addedpp_radio_tx_pulses()topp_radio.cpp— switches CC1101 to TX mode, bit-bangs OOK pulses on GDO0, returns to RX. In packet detail view: SELECT = save to SD, RIGHT = replay captured signal 3× via CC1101. Signal replay confirmed working on real hardware.ProtoPirate — Nosifer logo bar — "ProtoPirate" title in Nosifer drip font added as permanent logo strip between freq/RSSI header and content area. Appears in all views viafixdraw_header().PP_LOGO_H=28,PP_CONTENT_Hupdated to account for logo. Splash screen removed.ProtoPirate signal replay confirmed on real hardware — captured SubGHz packet replayed via CC1101 TX, target device responded correctly. Full capture → save → replay loop working end-to-end.hwRAM overflow fix — PPPacket pulse buffer — addingfixraw_pulses[256]per packet toPPPacketcaused 40KB RAM spike (32 history entries × 1280 bytes each). NRF24 and SD card both failed at boot due to heap corruption. Fixed by reducing toraw_pulses[64](64 pulses sufficient for all tested SubGHz protocols) andPP_HISTORY_MAXfrom 32 to 16. RAM back to 45%. All radios and SD confirmed passing radio test. -
v1.3 2026-05-29 radioSPI + BLE Jammer fixed 9 changes ▶✓ done — NRF24 #3 fixed — schematic confirmed CE=GPIO14 / CSN=GPIO21 (shared with IR, not GPIO41/42). All 3 NRF24 modules now passing radio test ✅fix⧗ in progress — verify SD loot saves (EAPOL .hc22000, BLE Predator recon log, Flock You output) with fixed radioSPI busfix✓ done — BLE Jammer working —new
bjRadiolocal RF24 object per namespace,jamSPIcore 0 task usesradioSPI, SELECT/UP/DOWN buttons mapped to toggle/mode change✓ done —fixnrf24_config.cppSPI claim/release cleaned up — removedSPI.end()/SPI.begin()pattern, replaced with CS pin management only on sharedradioSPIbus⧗ pending —newPCF_BTN_BACK_PINduplicate withPCF_BTN_LEFT_PINon P3 — back button not independentradio test — NRF2 + NRF3 + SD all failing — diagnosed three root causes: (1) NRF3 CE/CSN wrongly assigned to GPIO41/42 — schematic confirmed correct pins are CE=GPIO14 / CSN=GPIO21, shared with IR TX/RX. IR disabled (hwDIV_HAS_IR=0) to free pins for NRF3. (2) NRF2 and NRF3 had noSPI.begin()call — radio test only initialised bus for NRF1. (3) SD passed globalSPIobject toSD.begin()which was initialised with NRF1 CSN as default CS — caused silent SD failure.radioSPI bus overhaul — all radios and SD fixed — introduced singlefixSPIClass radioSPI(HSPI)started once insetup()with CS=-1. All three NRF24 modules callRF24::begin(&radioSPI)with their own CE/CSN. SD card usesSD.begin(SD_CS, radioSPI, SD_SPI_FREQ). Ranfix_sd.shpatching 9 files:HaleHound-DIV.ino,eapol_capture.cpp,saved_captures.cpp,wifi_attacks.cpp,ble_predator.h,captive_portal.h,flock_you.h,iot_recon.h,pp_settings.cpp. Radio test result: NRF1 ✅ NRF2 ✅ NRF3 ✅ SD ✅ CC1101 ✅cyd_config_div.h + nrf24_config.cpp overhaul — fixed all brokenfixDIV_*aliases in shim. AddedRADIO_SPI_SCK/MISO/MOSIandNRF24_CE/CSNaliases required bynrf24_config.cppandbluetooth_attacks.cpp. Cleaned upnrf24ClaimSPI()/nrf24ReleaseSPI()— replacedSPI.end()/SPI.begin()bus restart pattern with CS pin management only.nrf24Radio.begin(&radioSPI)called once per use. Addedshared.hinclude topp_settings.cppandnrf24_config.cpp.BLE Jammer fixed and fully working — root cause was globalfixnrf24Radioobject shared between BleJammer namespace (core 1) and jam task (core 0) with two different SPIClass instances (radioSPIand localjamSPI) causing RF24 internal state corruption. Fix: declaredstatic RF24 bjRadio(NRF24_CE, NRF24_CSN)local to BleJammer namespace, core 0 task usesradioSPIdirectly. Added PCF8574 button bindings: SELECT = toggle jam on/off, UP/DOWN = cycle mode, BACK = exit. CP2102 UART port confirmed for serial monitor (separate from native USB flashing port). -
v1.2 2026-05-25 documentation update 1 change ▶documentation updated — full project log reviewed and backfilled with ProtoPirate port architecture work from May 20: display/radio SPI bus separation,hw
spi_managerper-module exclusive access, CC1101setGDO()standardisation,detachInterrupt()cleanup pattern, anddiv_config.has single pin definition source. NRF24 #3 hardware investigation still open. -
v1.1 2026-05-21 NRF24 #3 investigation 2 changes ▶⧗ in progress — verify SD loot saves (EAPOL .hc22000, BLE Predator recon log, Flock You output)newNRF24 #3 investigation ongoing — GPIO 41/42 probed as replacement CE/CSN to avoid IR conflict (14/21 shared). Pogo-pin contact suspected as primary failure cause. Multimeter check on GPIO 41/42 after boot pending — should read >3V if software is driving them HIGH correctly.new
-
v1.0 2026-05-20 SPI bus overhaul 6 changes ▶✓ done — SD card fixed — was using globalfix
SPIobject instead of dedicatedradioSPIHSPI busProtoPirate port started — began porting ProtoPirate firmware modules to ESP32-DIV. Identified five core architecture problems from the CYD-to-DIV port: display and radio sharing one SPI bus causing white screen when radios initialise, no per-module bus arbitration causing crashes across modules, missing touch hardware replaced by PCF8574, CC1101 deaf after first use due to missinghwsetGDO()call, and interrupt leakage causing "works once" failures. Establisheddiv_config.has single source of truth for all pin definitions withcyd_config_div.has compatibility shim.ProtoPirate port — bus architecture fixed — separated display SPI (VSPI) from radio SPI (HSPI) to eliminate white screen on radio init. Implementedfixspi_manager— exclusive per-module bus access (one device on the bus at a time) to stop modules crashing each other. Standardised CC1101 init pattern:setSpiPin()→setGDO(GDO0, GDO2)→Init()on every module entry. MissingsetGDO()was root cause of CC1101 being deaf after first module use. AddeddetachInterrupt()+ buffer flush on every module exit — fixed "works once then breaks" failure across all interrupt-driven modules.ProtoPirate port — SPI bus overhaul — introduced dedicatednewSPIClass radioSPI(HSPI)global for all radios and SD card. AllRF24::begin()calls updated to pass&radioSPI. SD card re-initialised withSD.begin(SD_CS, radioSPI, SD_SPI_FREQ). Previously using globalSPIobject caused SD to silently fail after any radio init.cyd_config_div.h fixed — added all missingfixDIV_*aliases,RADIO_SPI_*defines, andNRF24_*pin mappings required by ProtoPirate modules. Fixedpp_settings.cppmissingshared.hinclude. Ranfix_sd.sh— patched 9 files across codebase to useradioSPI.SD card confirmed working — boot radio test shows SD ✅. Root cause was SPI object mismatch — globalnewSPI(VSPI) vs dedicatedradioSPI(HSPI). NRF24 #1 ✅ NRF24 #2 ✅ NRF24 #3 ❌ — failure isolated to GPIO 41/42 assignment or pogo-pin contact on shield. -
v0.9 2026-05-19 on-device testing 1 change ▶on-device testing — HaleHound modules — confirmed button navigation working across all ported modules afterfix
btn_update()cache fix. PCF8574 UP/DOWN/LEFT/RIGHT/SELECT inputs stable. Began on-device validation of WiFi pack (Auth Flood, EAPOL Capture, Karma, Captive Portal) and BT+NRF24 pack (BLE Predator, Lunatic Fringe, MouseJack). SD loot saves under test (EAPOL.hc22000, BLE Predator recon log). -
v0.8 2026-05-16 HaleHound modules ported 6 changes ▶✓ done — HaleHound modules ported: WiFi (Auth Flood, EAPOL, Karma, Captive Portal), BT+NRF24 (BLE Predator, Lunatic Fringe, Phantom Flood, AirTag Replay, NRF Sniffer, MouseJack), SIGINT (Flock You, WiFi Guardian, BLE Watchdog, SubGHz Sentinel)new✓ done — test all new modules on-device — button nav confirmed working across all modules after btn_update() cache fixfixHaleHound module port — WiFi pack — ported Auth Flood, EAPOL Capture, Karma Attack, Captive Portal (GARMR) from HaleHound-CYD. All touch zones remapped to PCF8574 5-button input (UP/DOWN/LEFT/RIGHT/SELECT). EAPOL saves tonew
/eapol/<SSID>.hc22000(hashcat -m 22000 ready). Karma auto-deauths every 30s if no handshake. Credential logging to SD.HaleHound module port — BT + NRF24 pack — ported BLE Predator (scan → GATT recon → GATTS honeypot, loot to SD), Lunatic Fringe (AirTag/FMDN/SmartTag/Tile tracker scanner), Phantom Flood (FindMy OF key rotation), AirTag Replay (clone + replay), NRF Sniffer (Travis Goodspeed promiscuous, 126-ch hop, Core 0 task), MouseJack (HID++ injection, 5 payloads, LRC + CRC16).newHaleHound module port — SIGINT pack — ported Flock You (passive BLE scanner for Flock Safety ALPR cameras + Raven/SoundThinking sensors — OUI, name, manufacturer ID, GATT UUID fingerprinting), WiFi Guardian (deauth/disassoc flood detector, promiscuous mode), BLE Watchdog (advert flood detector, per-MAC rate tracking), SubGHz Sentinel (CC1101 RSSI sweep across 315/433/868/915 MHz, jammer alert at −60 dBm sustained).newbuild errors resolved + firmware flashed — fixed 7 compiler issues:fixWiFi.BSSID()API mismatch, BLEgetProperties()rename,getNative()->valpointer cast, CC1101SetMHZ→setMHZcase, MouseJack HID keymap C99 designated initialiser incompatibility with Xtensa GCC 8,btn_input.hredefinition conflict resolved by bridging to existinginput_read()API. Button event consumed-before-read bug fixed withbtn_update()cache. Clean build: 33.8% RAM / 55.6% flash. Firmware flashed via UART USB-C port. -
v0.7 2026-04-14 IR support 1 change ▶IR support added — TX (GPIO14) and RX (GPIO21) both working viafix
IRremoteESP8266. Raw capture and replay implemented. GPIO14 mutex handles NRF24 #3 CE conflict — NRF24 #3 deselected before IR acquire, restored on exit. RX requires NRF24 #3 CSN HIGH (GPIO21 shared). -
v0.6 2026-04-12 UI complete 1 change ▶UI complete — switched to portrait 240×320 (rotation=2). Cifertech-style menu: black background, cyan accent lines, left bar on selected item, separator lines, footer hints. Splash image resampled to 240×320 portrait. Splash used as menu background with transparent item overlay.new
-
v0.5 2026-04-11 display + buttons working 2 changes ▶display working — removed PSRAM flags. Fixed SPI bus conflict between TFT_eSPI and CC1101 (both defined globalfix
spisymbol — renamed CC1101 libdep). Added-DUSE_HSPI_PORT=1to give TFT dedicated SPI instance. Moved tft.init() before SPI.begin() for radios. Display boots cleanly.buttons working — I2C scan confirmed PCF8574 at 0x27 (not 0x20 as documented). Board also has IP5306 at 0x75. Button pin mapping confirmed via raw byte scan: UP=P7, DOWN=P5, LEFT=P3 (also BACK), RIGHT=P4, CENTER=P6. FixedfixUSER_SETUP_LOADEDflag blocking font loading in TFT_eSPI. -
v0.4 2026-04-10 first flash attempt 1 change ▶splash screen added — segfault.solutions logo converted to RGB565 PROGMEM. First flash attempt — board crashes with StoreProhibited on tft.init(). Root cause:new
-DBOARD_HAS_PSRAMflag — board has no PSRAM despite product page claim. -
v0.3 2026-04-09 HaleHound-DIV port started 2 changes ▶HaleHound-DIV port started — full PlatformIO port of HaleHound-CYD to ESP32-S3. Remapped all SPI pins from cifertech schematic. Replaced touch input with PCF8574 button driver. Landscape 320×240 display orientation.hwattack modules written — WiFi (8 modes), BLE (7 modes inc. CVE-2025-36911 WhisperPair), NRF24 (4 modes), Sub-GHz CC1101 (5 modes), EAPOL capture + Karma attack. SPI bus arbitration + radio test on boot.new
-
v0.2 2026-04-01 firmware research 1 change ▶firmware attempt failed — tried flashing JesseCHale's updated firmware but DIV v2 uses ESP32-S3 — chipset mismatch, incompatible with Hale's buildhw
-
v0.1 2026-01-15 project started 1 change ▶started — researching ESP32 DIV v2.1, reviewing hardware and firmwarehw
pin conflicts & resolutions
Several GPIOs are shared between peripherals. Each conflict is handled in firmware — modules check out exclusive access before use and restore state on exit.
| gpio | peripheral A | peripheral B | resolution |
|---|---|---|---|
| 14 | NRF24 #3 CE | IR TX | GPIO14 mutex — NRF24 #3 deselected (CE LOW, CSN HIGH) before IR acquire. IR release restores NRF24 CE. Cannot use NRF24 #3 and IR simultaneously. → ir_acquire() / ir_release() in firmware |
| 21 | NRF24 #3 CSN | IR RX | NRF24 #3 CSN held HIGH during IR RX capture so the radio is deselected and the pin floats for the IR receiver. → digitalWrite(NRF3_CSN, HIGH) before IR capture |
| HSPI bus | TFT display (SCK=36, MOSI=35, MISO=37) | NRF24 ×3, CC1101, SD card (SCK=36, MOSI=35, MISO=37) | Dedicated SPIClass radioSPI(HSPI) instance for all radios and SD. TFT uses the same HSPI pins but with -DUSE_HSPI_PORT=1 giving it a separate SPI class instance. Each device selected via individual CS pin.→ radioSPI.begin() separate from TFT_eSPI init |
| CC1101 spi symbol | TFT_eSPI library (global spi) |
CC1101 library (global spi) |
CC1101 libdep spi symbol renamed in dependency to avoid link-time collision with TFT_eSPI's global spi object.→ CC1101 library patched in lib/ |
links